When services were taken down on Sony's PlayStation network and Microsoft's Xbox Live network on 25 December 2014, the mood of many gamers who intended to spend their Christmas holidays playing online games was spoiled. The reason for the stoppage was overloading by a 'distributed denial of service attack', aka a DDoS attack.
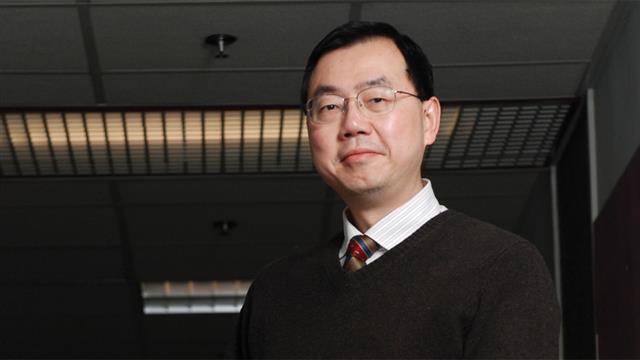
Prof. Lau Wing-cheong of the Department of Information Engineering explains, 'A DDoS attack is meant to interrupt or suspend the services of a server or website. It's called “distributed” because the incoming traffic flooding the victim originates not from one source, but hundreds of thousands of different sources.'
Hong Kong people are no strangers to DDoS attacks. Last year a popular voting website in the city was crippled by a massive 200Gbps DDoS attack. Professor Lau says, 'If your computer, smartphone or TV box is infected with a computer virus or malware, hackers can not only steal your personal information, but can also remotely control such an Internet endpoint to do something harmful, such as sending out junk mail and launching DDoS attacks. The computers under their control are called Bots.'
In addition to cyber mischief, DDoS attacks have been used for extortion. Professor Lau explains, 'There are betting sites overseas where gamblers may try their luck before a competition such as a World Cup match. People could blackmail these websites, threatening attack and prolonged paralysis.' DDoS attacks can also be used to launch more sophisticated attacks, such as taking down a certain website and making a fake one to spread misleading or false messages or to achieve other purposes.
Professor Lau says that defending a site against DDoS attacks is not an easy task. The so-called 'clean slate approach', which means replacing the current internet infrastructure and protocol with new ones, is one of the more ideal solutions. Research on the future architecture of the internet has been conducted around the world. But the widespread adoption of a new internet architecture is not something that will happen in the near future.
The chief targets of DDoS attacks are service providers rather than individuals. But that doesn't mean that individual users are immune. Professor Lau points out that cloud services and mobile apps have more serious implications for individual users. He explains, 'Now almost everyone has a smartphone. But some mobile apps may be written by one or two students. Because of limited resources and awareness, these apps may not be very safe in terms of cybersecurity.'
Professor Lau says that cybersecurity is one of the recent focuses of the Department of Information Engineering. The department not only makes this a main area of research, but also sees it as a key element of its curricula, with an aim to improving students' technical know-how and awareness about this subject. When programmers design a system or write a programme, they normally attach the greatest importance to its efficiency and its ability to run smoothly. They may not prepare it well enough for a worst-case scenario brought about by active and systematic attacks. And hackers will constantly look for the vulnerabilities of a programme and bottlenecks of a system to trigger corner cases, causing the programme to run a hundred or a thousand times slower than normal.
The future Internet of Things also presents a new challenge to cybersecurity. It's because more and more household devices such as home monitors, lighting systems, and thermostats are connected to the Internet. Malicious actors are shifting their focus to devices beyond the commonly-targeted personal computers. In view of this trend, mobile security is one of the recent research interests of the Mobile Technologies Centre led by Professor Lau.
This centre focuses on the research of mobile technologies and its applications. Other research interests include cloud services, radio-frequency identification, decentralized social network. Professor Lau says, 'We've developed some programmes that can scan and detect vulnerabilities of mobile apps and social networks. The industry is interested in this technology and hope that we can help them to identify problems of their apps.'
He adds, 'The most rewarding thing for us as members of the Chinese University is to see that our research results can solve problems for the industry through knowledge transfer and make an impact on society.'